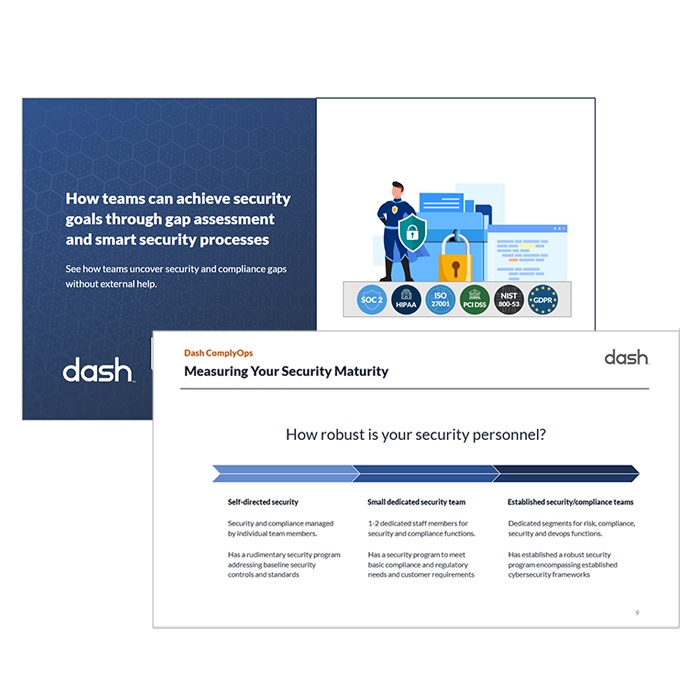
How teams can achieve security and compliance goals through gap assessment
This FREE report reveals how teams the gap assessment and smart security processes needed to meet security and compliance goals faster without additional overhead.
– Determine security gaps
– Implement effective security operations
– Meet compliance requirements for HIPAA, SOC 2, ISO…
How teams can achieve security and compliance goals through gap assessment
This FREE report reveals how teams the gap assessment and smart security processes needed to meet security and compliance goals faster without additional overhead.
– Determine security gaps
– Implement effective security operations
– Meet compliance requirements for HIPAA, SOC 2, ISO…
SEND ME THE FREE GUIDE
SEND ME THE FREE GUIDE
Learn How You Can Set Robust Compliance Operations
Now sure about security next steps? This guide walks through evaluating your security baseline and building a compliance roadmap. See how a structured gap assessment and smart security controls provide the foundation for strong compliance operations.
Find Security Gaps & Improve Compliance Processes:
✅ Increase clarity on your current posture
✅ Create a structured, prioritized plan
✅ Set predictable compliance workflows
✅ Reduce overhead
✅ Streamline SOC 2, HIPAA, ISO 27001, etc
Jacob Parsell
CTO, Redsson
Let’s Talk About Security And Compliance
If you are stuck in a never-ending cycle of nervously responding to customer security requests, or constantly putting out fires related to security requirements…
For many teams, compliance becomes a cycle of rushing to complete tasks, gathering evidence at the last minute, and trying to interpret what each framework actually requires.
Gone are the days of…
…Receiving security questionnaires and rushing to implement missing standards.
…Guessing which tools, solutions, and security settings should be implemented.
…Searching for information and security procedures across the organization.
…Managing multiple static spreadsheets to track security and compliance requirements.
Security and compliance should be structured so that your team has a repeatable playbook. More importantly, when developed with care, security programs can be sustainable and easy to follow.
Isn’t it time you finally cracked the compliance operations process?

The problem isn’t effort.
It’s the lack of a structured process that brings everything together.
Once you understand your security baseline and how it maps across these frameworks, the entire picture changes.
You know what’s already in place, where the real gaps are, and what matters most for upcoming audits and customer reviews ahead.
In this guide with provide the practical steps for:
1. Evaluating your organization’s security program, no matter your security maturity, size, or capabilities.
2. Improving your team’s administrative policies, technical controls, and security standards.
3. Empower your team to set proper security tasks and workflows, and help you maintain Baseline Security, HIPAA, SOC 2, ISO 27001 and more.
With all of this information, your team will be better prepared to address security gaps, determine long term objectives, and start meeting your security goals.
We have helped hundreds of organizations build sustainable security programs, all WITHOUT additional staff.
“Dash ComplyOps helped our team streamline the HIPAA compliance process. Our development team has become more knowledgeable about security and compliance”
“Dash ComplyOps helped ensure that our market leading real-world vital data platform for healthcare providers and pharmaceutical clinical trials meet security and policy standards for compliance.”
Access A System For Better Security Management
In the FREE Gap Assessment Guide, we have put together a full report and assessment plan from years of experience helping teams build security programs.
Whether you are a small startup with 3 employees looking to set baseline security, or a larger organization building out a new security program for SOC 2, HIPAA, ISO 27001 or similar, this Gap assessment workflow can reduce your security planning and implementation from months to weeks.
Our process assesses your security program, no matter the current state of your IT security program.
This resource includes workflows for determining current security posture, as well as:
✅ Assessment criteria based on your current security goals.
✅ Recommendations for meeting baseline security controls.
✅ Options for security implementation.
✅ Best practices for streamlining security operations.
Security Gap Assessment and Smart Workflows
Access the FREE guide.